The Algorithmic Vanguard: OpenAI's GPT-5.4-Cyber and the Redefinition of Digital Fortification
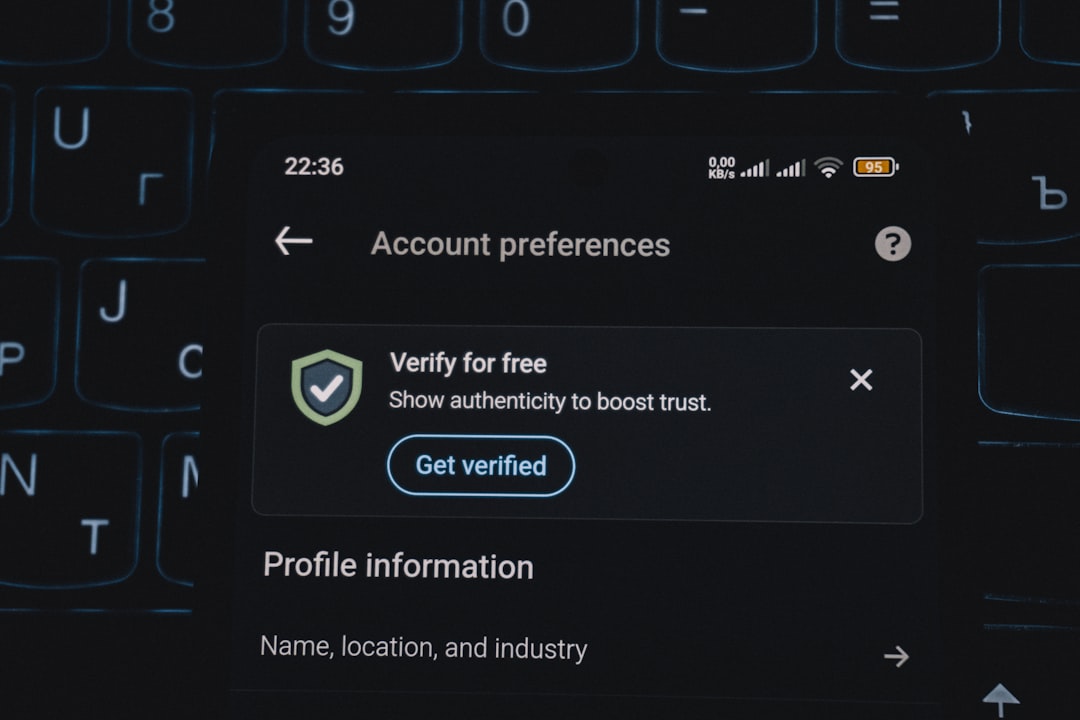
Explore the profound implications of OpenAI's GPT-5.4-Cyber and its 'Trusted Access for Cyber' program. This analytical deep dive dissects how advanced AI is reshaping cybersecurity, the ethical complexities of curated access, and the long-term trajectory of human-AI synergy in safeguarding our digital future. #Cybersecurity #AIdrivenDefense #TrustedAccess #GPT5Cyber